Recovering Cleared Browser History - Chrome Forensics
Hello naughty sysadmin... I've been watching your search history this Summer O_o
How do you detect when a user deletes their chrome history and is there a way to forensically recover it? The answer is… it depends. 😈
A good indicator for recovering what a user was doing when they deleted their chrome browser history is by checking inside the C:\Users\<name>\AppData\Local\Google\Chrome\User Data\Default\Sessions folder. The two files you need to look at are named:
- Session_<Webkit/Chrome date>
- Tabs_<Webkit/Chrome date>
The session file stores session information and the tabs file stores what tabs they had opened. In a certain situation when a user CLEARS their Chrome history, what they were browsing can persist within these files.
There are a few potential cases that could have occurred, and we will go through all of them:
- A user cleared their history and did not use Chrome since
- A user clears their history and re-opened ONE new session
- A user clears their history and re-opened several sessions since
Scenario 1: User cleared their history and did not use Chrome since
When a user clears their Chrome history (by all time or even by the last hour) and has not opened Chrome since, everything they were looking at during the session is STILL STORED inside the session files. This is great news because the session file is dated with the exact Webkit/Chrome timestamp in the name of the file. Why is this the case? I don't work for Google so I have nfi.
In this instance the files I’m looking at were named:
- Session_13311227045752079
- Tabs_13311227047407569
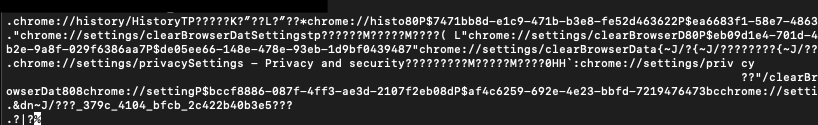
Using this time converter (https://www.epochconverter.com/webkit), you can see the time when the user “exited” the session was at 2022-10-26T03:04:05Z. You can see a full timeline of what the user did by viewing the contents of the file. Please note there are no corresponding “timestamps” captured within this file unfortunately. This is what the file looks like:
Scenario 2: A user clears their history and re-opened ONE new session
- C:\Users\<user>\AppData\Local\Google\Chrome\User Data\Default\Favicons
- C:\Users\<name>\AppData\Local\Google\Chrome\User Data\Default optimization_guide_prediction_model_downloads/b0b608bd-983f-4cf9-aee4-99fc96c39371/global-entities_metadata







Comments
Post a Comment