Forensic Detection of Files Deleted via SDelete
Russian nation-state adversaries abuse the tool “sdelete” to perform file deletion of their attack files. Sdelete is still being used by IRON HEMLOCK (APT29) in 2022 as a part of defence evasion. The tool “sdelete” was created by Mark Russinovich and is used to securely prevent files from being recovered through deleting the file and overwriting the file data in unallocated portions of the disk. What's annoying about this tool is it shows artefacts with overwritten filenames "AAAAAA.AAA" instead of the original name.
This is a quick forensics write-up demonstrating that you can in fact, recover the original file names from analysis of $J.
DETECTION METHODOLOGY
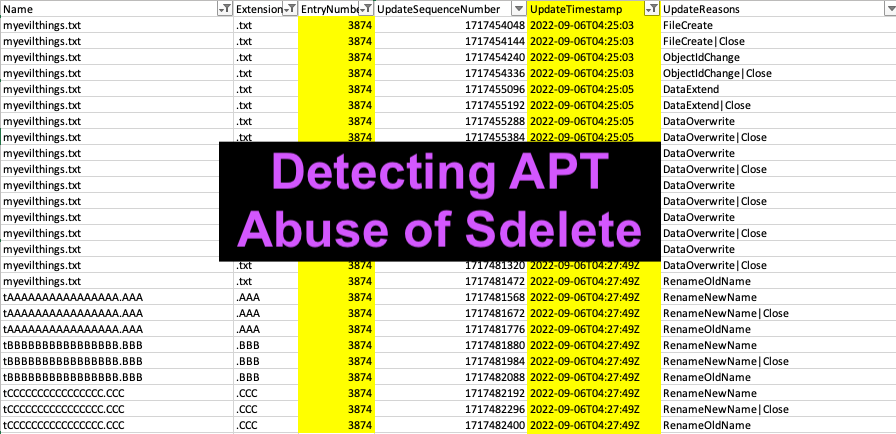
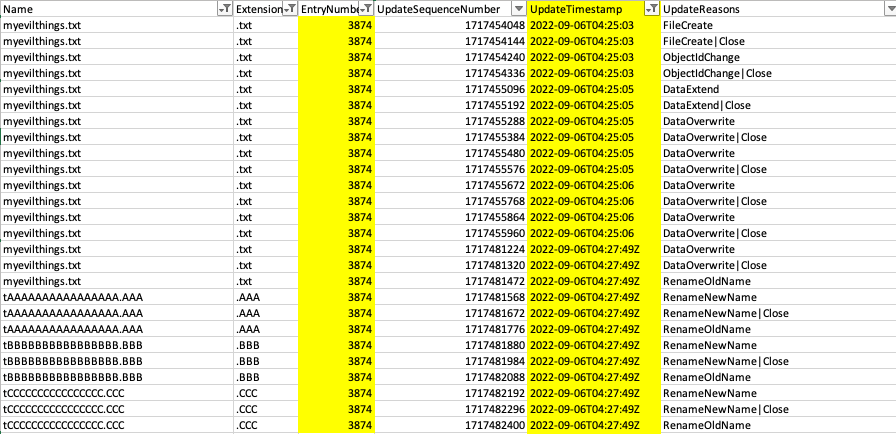
When sdelete is utilised, it leaves obvious traces in the USN Journal, $J file where 26 unique entries will be created in alphabetic order as pictured below. This is a dead giveaway that “sdelete” was utilised by the threat actors.
The best way to review the $J file is to parse by the Entry Number. This corresponds to the same number in the original MFT entry which will be created when the file is first created on disk. Please note, in the case where sdelete is utilised, the MFT record will likely be overwritten by another file (on busy disks).
When you filter by the entry number, you will see the original file name that the threat actors utilised (pictured below).
This is the methodology for analysing $J for the files deleted via “sdelete”:
1. Determine “sdelete” was utilised on the host
This can be done by looking at a series of artefacts of execution OR through analysis of $J and noting 26 alphabetical files created with the same timestamp corresponding to the operations:
- RenameNewName / RenameNewName | Close
- RenameOldName
2. Filter by the EntryNumber
This is to make sure you are looking at the $J entries that map to the same file ;)
3. Determine the original file name
These will be listed under the following $J update operations:
- FileCreate / FileCreate | Close
- ObjectIDChange / ObjectID | Close
- DataExtend | Close
- DataOverWrite | Close
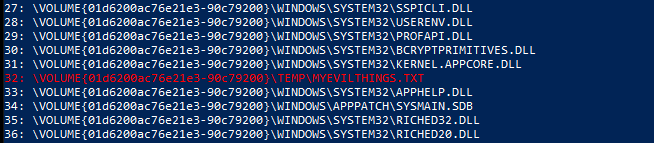
4. Check prefetch files
If this is a workstation and the corresponding prefetch files haven’t been removed, this will also reveal the original file name:
What about $I30?
One question you might have is … what about filename artefacts that might be left in the directory file entry slack space? Typically, this is a good detection for other file wipers, but when I tested this and reviewed slack space and parsed out the $I30, this file had been fully purged #notUwU
References:



Comments
Post a Comment