Malware Analysis: Slingshot APT Exposed From 6 Years of Hiding
Designed for cyber espionage, Slingshot APT (Advanced Persistent Threat) has hidden from researchers for over 6 years and has infected at least 100 hosts worldwide in the Middle East and Africa.
The malware used exploits on Mikrotik routers and has been listed as one of the most sophisticated attacks discovered rivalling Project Sauron (nation-state funded malware) and Regin (the malware that infiltrated Proximus Group). Due to the sophisticated nature of Slingshot APT, Kaspersky Labs report suspects the malware has received significant resource and financial backing and was the result of a highly-targeted attack plan. Slingshot APT is able to log user data, collect open windows, keystrokes and network data among other functionalities.
Slingshot APT works by replacing a legitimate Windows DLL (scesrv.dll or spoolsv.exe) related to Virtual File System, with a malicious one. There are two embedded loaders in Slingshot in the case of the first loader failing, the second loader will be triggered. Running with SYSTEM privileges, the internal logging system of Slingshot then determines if there is any kernel-mode payload available before running the loaders. To avoid system detection or additional logging, the ETW-logs are renamed and for all Security and System logs, the extension ‘.tmp’ are appended. Upon execution of the loader, the extensions are removed for further obfuscation.
The module Cahnadr is then successfully loaded into kernel mode (kernel-focused payload) by saving the driver on the disk.
(Source: Kaspersky)
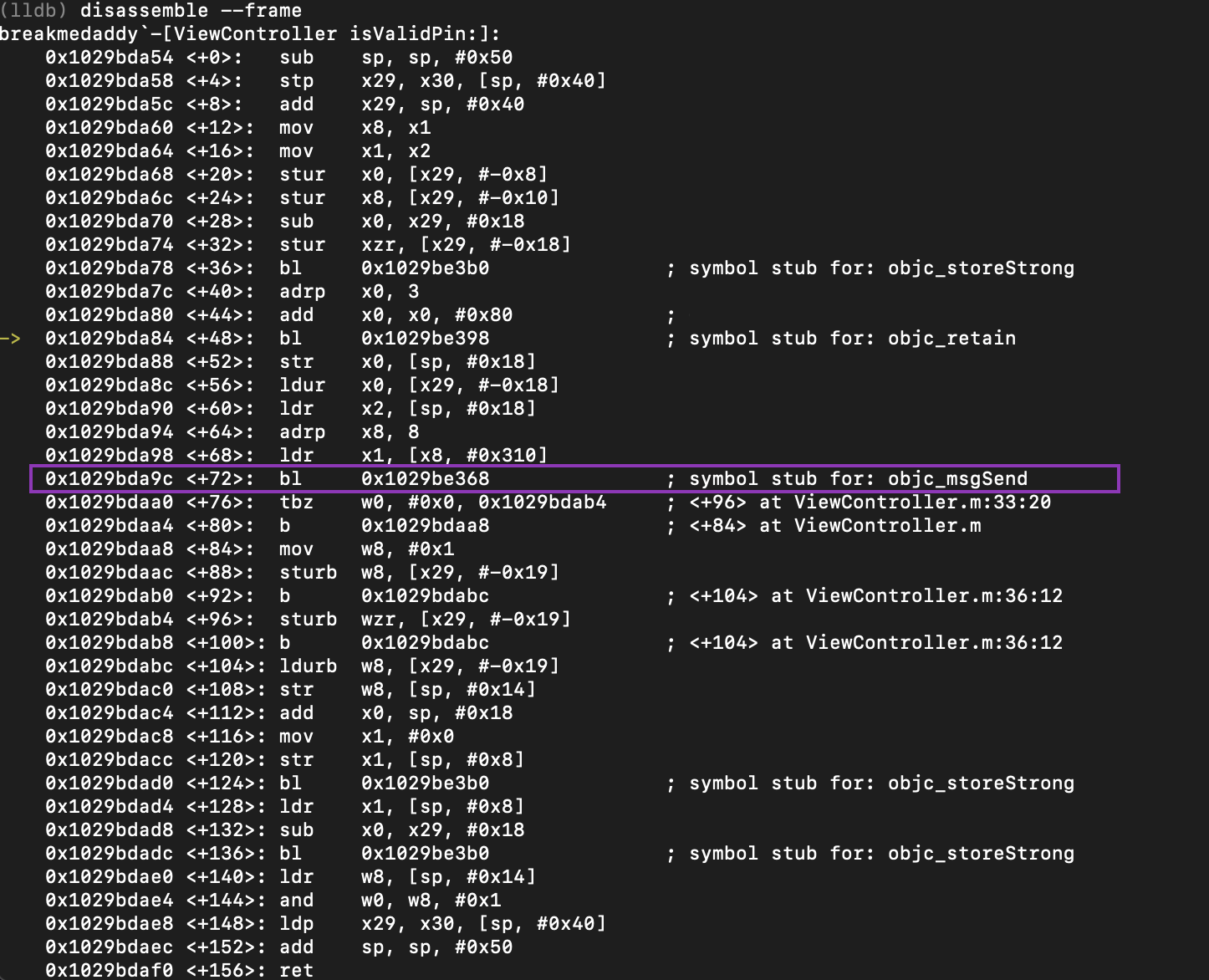
The code snippet above demonstrates that the malicious payload is called through DeviceIoControl with the code ‘0x222000’. This allows the module to access the System Worker Threads pool – otherwise, the module will exploit other vulnerable drivers found in the system that allow write-access to MSR registers. These exploits include (CVE-2007-5633, CVE-2010-1592, CVE-2009-0824). The writing to the MSR registers will successfully allow a function call to the malicious module Cahnadr before another malicious module GollamApp is also extracted.
The loader then compresses the original file in the malware’s data section to retain the same size as the original DLL. The entry points are then rewritten to point to the added malware modules which then begin to execute. Once the malicious payloads have been executed, the malware then restores the original scesrv.dll or spoolsv.exe back to memory.
There are two main modules downloaded by Slingshot –
Cahnadr and GollumApp. Cahnadr is kernel-centric and is the main orchestrator
of the malware – giving GollumApp the ability to interact with the system.
Features of Cahnadr include initiating checks to see if the kernel has received
patches through CheckSum and TimeStamp values, rootkit actions, injection of
user-mode payloads, facilitating network communications, notifying other
modules (GollumApp) about process-related events and monitoring other network
devices as well as sniffing the protocols: ARP, TCP, UDP, DNS, ICMP and HTTP.
Programmed in C, Cahnadr provides the malware full access to the hard drive and OS functionalities. API functionalities are also offered by Cahnadr including direct disk access (read/write), raw memory address read/write and code injection into processes as a separate thread.
In terms of network access, Cahnadr checks the ASK flag in TCP to identify HTTP traffic. Cahnadr allows the following functionalities to be passed to GollumApp including ARP queries, ARP replies, custom network packages (with fields all customized from the Ethernet-layer) and supports IEEE 802.11 standard (allowing WiFi frame operations).
Programmed in C, Cahnadr provides the malware full access to the hard drive and OS functionalities. API functionalities are also offered by Cahnadr including direct disk access (read/write), raw memory address read/write and code injection into processes as a separate thread.
In terms of network access, Cahnadr checks the ASK flag in TCP to identify HTTP traffic. Cahnadr allows the following functionalities to be passed to GollumApp including ARP queries, ARP replies, custom network packages (with fields all customized from the Ethernet-layer) and supports IEEE 802.11 standard (allowing WiFi frame operations).
GollumApp
is the main user mode payload injected into services.exe as a separate
thread, while maintaining interaction with Cahnadr. The purpose of GollumApp is
to collect network-related data (routing tables, configurations, proxy
servers), notifications, passwords saved in browsers (FireFox, IE), key
logging, hard disk partitions and USB devices.
Mikrotik provides a software called Winbox
Loader for their customers to download DLLs from the
router’s file system which are directly loaded into the computer’s memory. An
additional library ip4.dll was found to be added onto the router by the
attackers which is linked to a Trojan-Downloader related to Slingshot.
The potency of Slingshot APT includes its unique ability to evade detection through module encryption, direct system service calls (to bypass security-product hooks) and anti-bug/patch-detection functionalities. In face of detection, Slingshot is also able to initiate shut-down of tasks and components but also ensuring the tasks are completed.
The potency of Slingshot APT includes its unique ability to evade detection through module encryption, direct system service calls (to bypass security-product hooks) and anti-bug/patch-detection functionalities. In face of detection, Slingshot is also able to initiate shut-down of tasks and components but also ensuring the tasks are completed.
The malware is highly-advanced and ‘elegant’ in its
ability to combine system components in a long-term focused and effective
manner. Designed to avoid detection and to be sustainable, the malware has successfully
evaded detection – also suggesting that it was created and funded by a
highly-skilled actor. Further, samples of the malware were marked as ‘version
6.x’ suggesting that the malware may have predated 2012. Currently, nothing further
is known of the creators other than the use of perfect English suggesting that
the actors came from an English-native origin and the actors’ penchant for Lord
of the Rings as seen in the references Gollum and Smeagol.
For remediation, Mikrotik router users are recommended to upgrade to the latest firmware version possible as further details of the malware are released. Kaspersky Labs has informed Mikrotik of the malware and Winbox no longer downloads DLLs from the router to the user’s computer.
For remediation, Mikrotik router users are recommended to upgrade to the latest firmware version possible as further details of the malware are released. Kaspersky Labs has informed Mikrotik of the malware and Winbox no longer downloads DLLs from the router to the user’s computer.
Countries Affected
Kenya, Yemen, Libya, Afghanistan, Iraq, Tanzania,
Jordan, Mauritius, Somalia, Democratic Republic of the Congo, Turkey, Sudan, United
Arab Emirates





This comment has been removed by the author.
ReplyDelete